AWS CloudTrail
AWS CloudTrail is a service that enables governance, compliance, operational auditing, and risk auditing of your AWS account. With CloudTrail, you can log, continuously monitor, and retain account activity related to actions across your AWS infrastructure. CloudTrail provides event history of your AWS account activity, including actions taken through the AWS Management Console, AWS SDKs, command line tools, and other AWS services. This event history simplifies security analysis, resource change tracking, and troubleshooting. In addition, you can use CloudTrail to detect unusual activity in your AWS accounts. These capabilities help simplify operational analysis and troubleshooting.
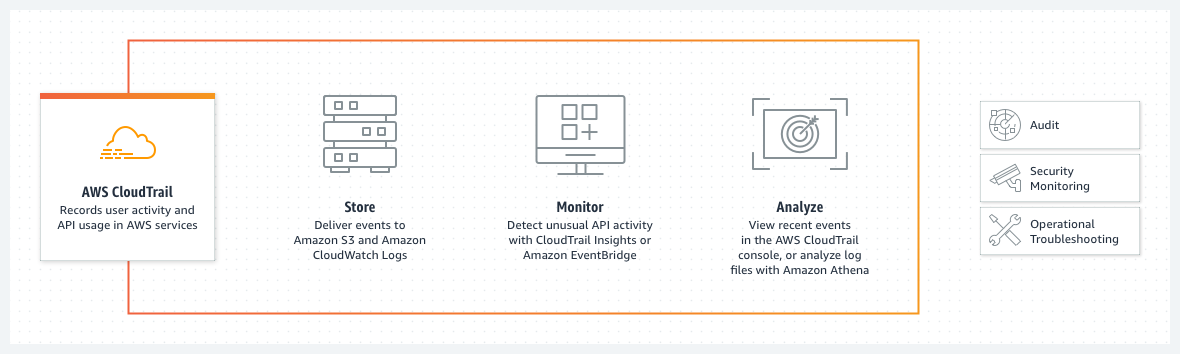
How It Works
Topics Discussed
Benefits
Simplified compliance
With AWS CloudTrail, simplify your compliance audits by automatically recording and storing event logs for actions made within your AWS account. Integration with Amazon CloudWatch Logs provides a convenient way to search through log data, identify out-of-compliance events, accelerate incident investigations, and expedite responses to auditor requests.
Visibility into user and resource activity
AWS CloudTrail increases visibility into your user and resource activity by recording AWS Management Console actions and API calls. You can identify which users and accounts called AWS, the source IP address from which the calls were made, and when the calls occurred.
Security analysis and troubleshooting
With AWS CloudTrail, you can discover and troubleshoot security and operational issues by capturing a comprehensive history of changes that occurred in your AWS account within a specified period of time.
Security automation
AWS CloudTrail allows you track and automatically respond to account activity threatening the security of your AWS resources. With Amazon CloudWatch Events integration, you can define workflows that execute when events that can result in security vulnerabilities are detected. For example, you can create a workflow to add a specific policy to an Amazon S3 bucket when CloudTrail logs an API call that makes that bucket public.
Use Cases
Compliance aid
AWS CloudTrail makes it easier to ensure compliance with internal policies and regulatory standards by providing a history of activity in your AWS account. For more information, download the AWS compliance whitepaper, "Security at Scale: Logging in AWS."
Security analysis
You can perform security analysis and detect user behavior patterns by ingesting AWS CloudTrail events into your log management and analytics solutions.
Data exfiltration
You can detect data exfiltration by collecting activity data on S3 objects through object-level API events recorded in CloudTrail. After the activity data is collected, you can use other AWS services, such as Amazon CloudWatch Events and AWS Lambda, to trigger response procedures.
Operational issue troubleshooting
You can troubleshoot operational issues by leveraging the AWS API call history produced by AWS CloudTrail. For example, you can quickly identify the most recent changes made to resources in your environment, including creation, modification, and deletion of AWS resources (e.g., Amazon EC2 instances, Amazon VPC security groups, and Amazon EBS volumes).
Unusual activity detection
You can detect unusual activity in your AWS accounts by enabling CloudTrail Insights. For example, you can quickly alert and act on operational issues such as erroneous spikes in resource provisioning or services hitting rate limits.
In your AWS account, you must have read privileges for AWS S3 buckets and AWS CloudTrail.
You can use this document to add a remote log collector to a AWS CloudTrail remote device (log source).
Pre-Deployment Considerations
AWS Account Information
Access your AWS console.
In the top, right corner, locate and copy your account number and corresponding region. You will need this information later.
Create A Remote Log Source
In Nexus, hover over Threat Management
 on the left-side nav.
on the left-side nav. Click Log Search.
Click External Sources.
Click the plus sign
 .
. If you do not have any log sources already created, then click Add a New Log Source.
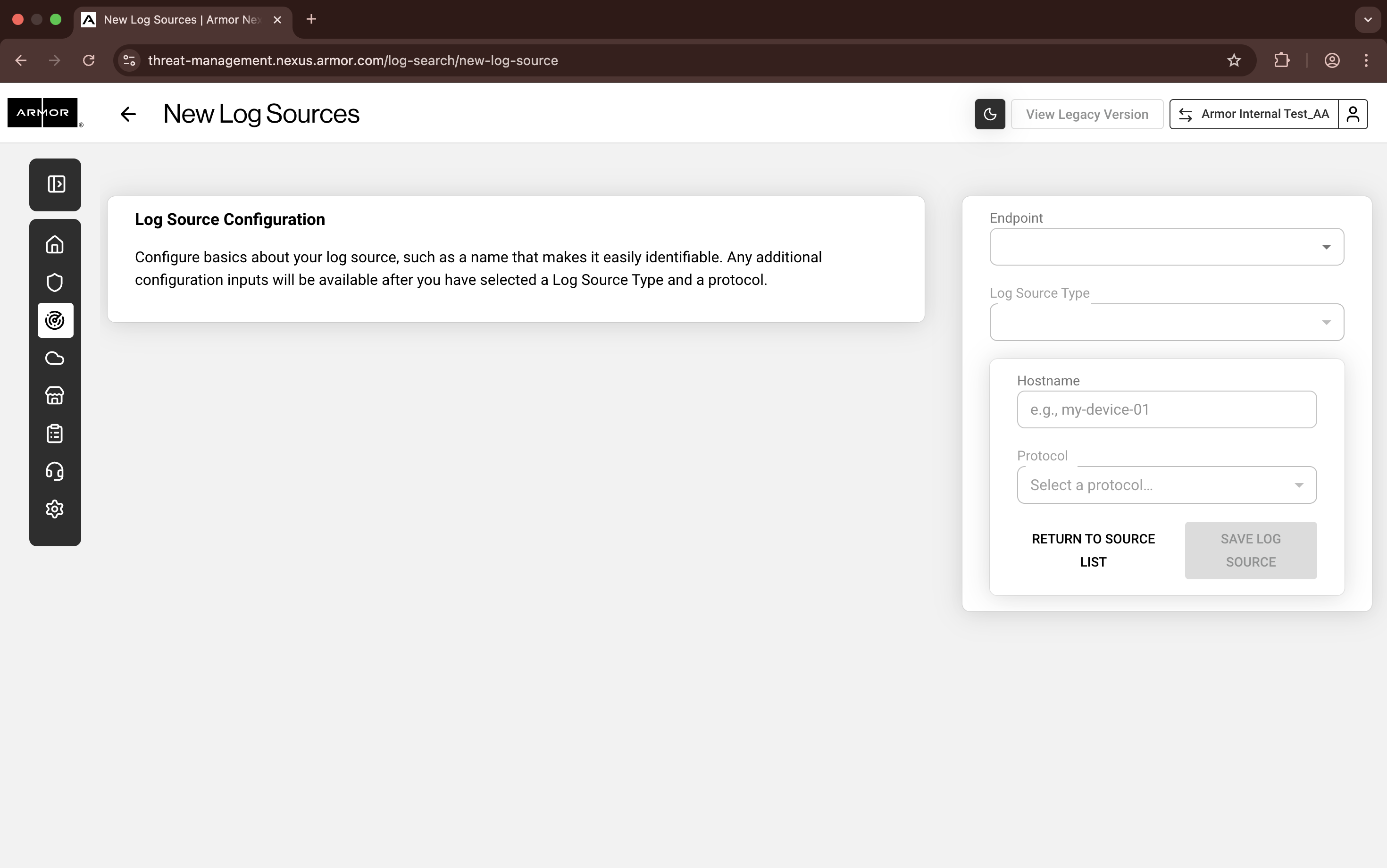
Nexus - Add New Log Sources
Complete the missing fields:
In Endpoint, select the available Armor Endpoint.
In Log Source Type, select Amazon AWS CloudTrail.
In Log Source Identifier, confirm that the listed system hostname matches the system for log collection.
This field will populate after you complete the Account Number field.
In Protocol, confirm that Amazon AWS S3 REST API is selected.
In Account Number, paste the AWS account number that you copied early. You must remove any dashes or hyphens ( - ).
In Region to Monitor, select the region that corresponds to the account number.
Click Save Log Source.
In the pop-up window, copy and paste the URL text. You will need this information in the AWS console.
Click Return to the Log Source List. You will be redirected to the External Sources screen.
In the External Sources screen, refresh the screen until the log source reaches an Online status.
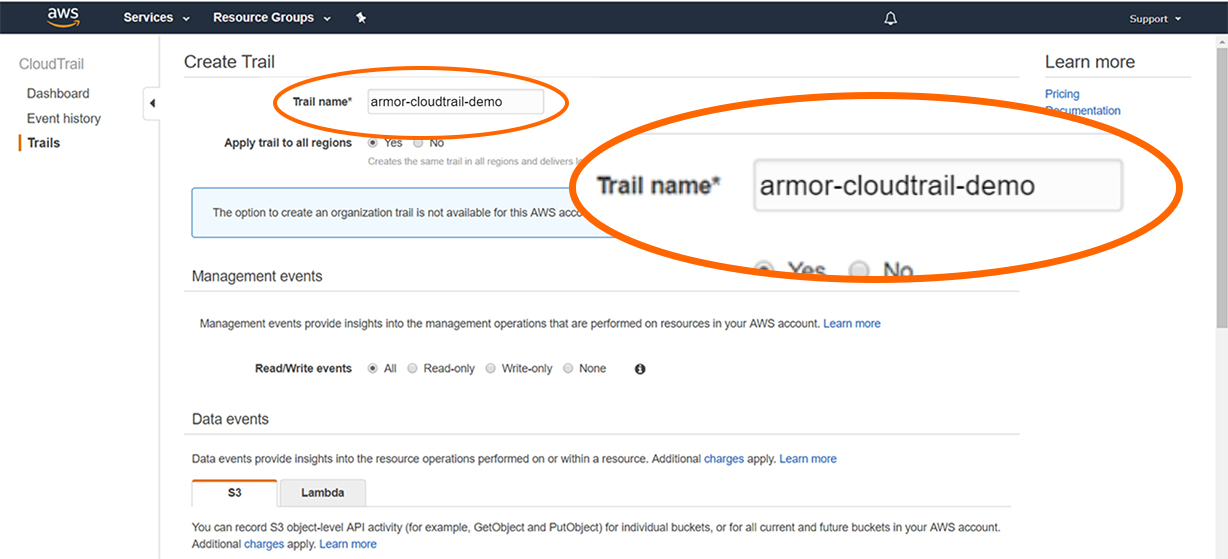
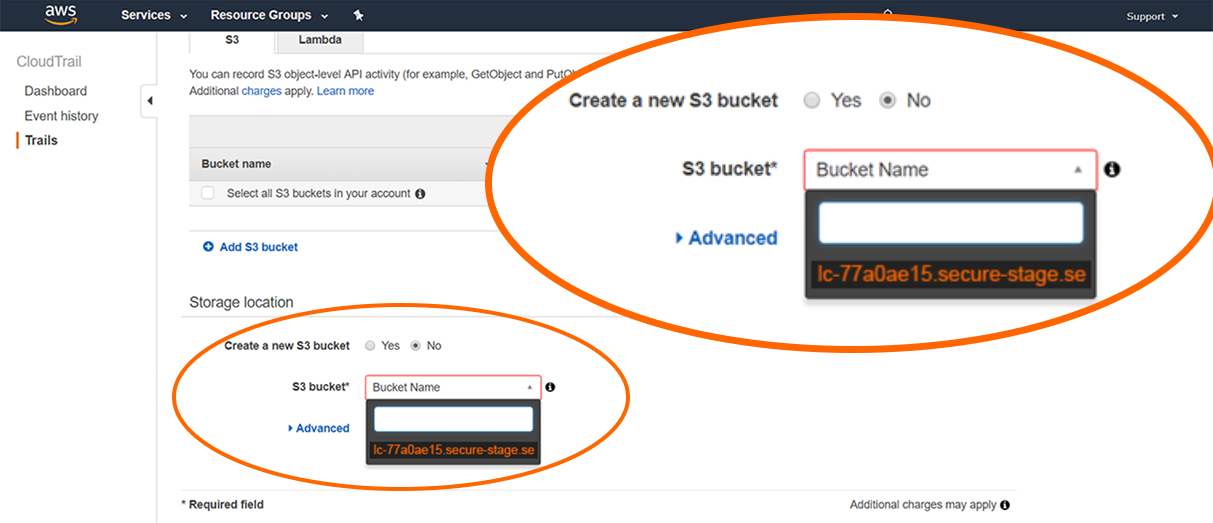
Create A New Trail And Sync Your AWS S3 Bucket
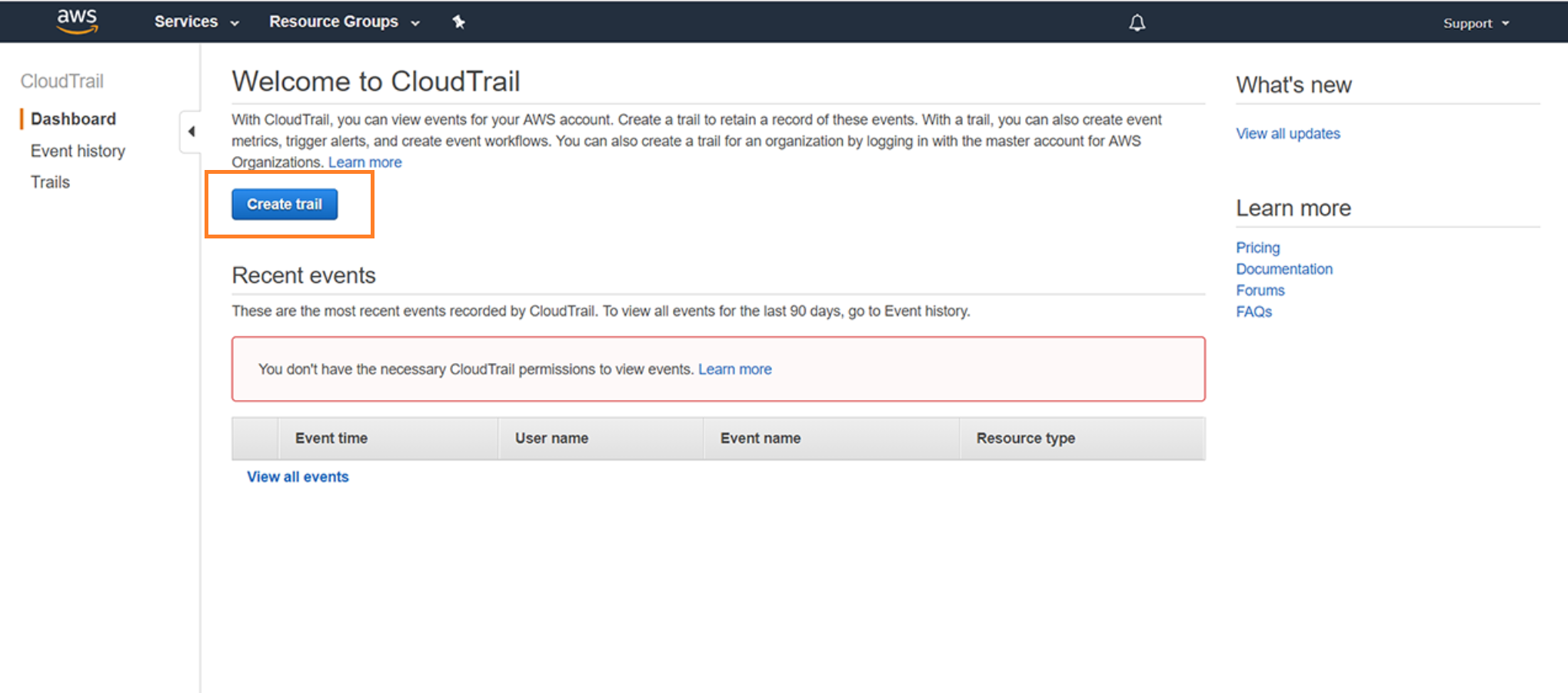
In the AWS console, navigate to the AWS CloudTrail section.
Update your account's region settings to match the region previously selected in Nexus.
Click Create trail. (You may first need to click View trails, and then click Create trail.)
For Apply trail to all regions, mark No.
In S3 bucket, paste the bolded URL text that you copied earlier from Nexus.
Click Create.
Verify Connection
In Nexus, hover over Threat Management
 on the left-side nav.
on the left-side nav. Click Log Search.
Click External Sources.
Locate the newly created remote log source.
Under Last Event, verify that a recent activity took place.
This status will indicate that the configurations were successful.
After you update your AWS account, it may take 30 minutes to display the updates.
Then click Log Search.
In the search field, enter your AWS account number surrounded by asterisks wildcards.
For example, you can enter *123456789123*
This action will display collected AWS CloudTrail logs.
Troubleshooting
If you are having issues adding a remote log collector to an AWS CloudTrail remote device, consider that:
You need to update your permissions in AWS.
You must have read privileges for S3 buckets and write privileges for AWS CloudTrail.
Your account must be assigned to the AWSCloudTrailFullAccess policy. To learn more the permissions (policies) for AWS CloudTrail, please see the documentation in AWS.
Ensure that the region you entered in Nexus matches your AWS account's region.
If you are having difficult searching for your logs, consider entering you AWS account number surrounded by asterisks wildcards, such as *123456789123*.