Create a Remote Log Relay Source - Cylance
Assumptions
The user has a Log Relay device online
The user is not blocking traffic on port TCP and UDP port
14015between the Cylance and the Log Relay
Setup
Upon activation of your account, you will receive an email with your login information for the Console.
Click the link in the email and go to the login page.
Login to the Console as an Administrator.
Select Settings > Application.
Record the displayed token. Download the installer by clicking either Windows or Linux or Mac OS X and then selecting the installation format.
Use the token when prompted during installation.
Note: CylancePROTECT Agent 1400 or higher must be installed on the endpoint before installing CylanceOPTICS for Windows.
For more info on CylanceOPTICS click here
Procedure
CYLANCEPROTECT SYSLOG SETTINGS
Click on Settings, then Application submenu.
When the page loads, scroll down to the INTEGRATIONS section of the page.
The following sections will provide details and descriptions for each sub heading in this section
EVENT TYPES
Syslog events have standard fields like timestamp, severity level, facility and a Cylance-specific payload (message). Examples provided in this section only contain the Cylance-specific message
SIEM (SECURITY INFORMATION AND EVENT MANAGEMENT)
Specifies the type of Syslog Server or SIEM that events are to be sent to. PROTOCOL This must match what you have configured on your Syslog server.
PROTOCOL
This must match what you have configured on your Syslog server. The choices are UDP or TCP. UDP is generally not recommended as it does not guarantee message delivery. TCP is the default and we encourage customers to use it.
TLS/SSL
Only available if the Protocol specified is TCP. TLS/SSL ensures the Syslog message is encrypted in transit from CylancePROTECT to the Syslog server. We encourage customers to checkmark this option. Be sure your Syslog server is configured to listen for TLS/SSL messages.
IP/DOMAIN
Specifies the IP address or fully-qualified domain name of the Syslog server that the customer has setup. Consult with your internal network experts to ensure firewall and domain settings are properly configured.
PORT
Enter Port 14015 log relay will listen for messages.
SEVERITY
Specifies the severity of the messages should appear on the Syslog server. This is a subjective field, and you may set it to whatever level you like. The value of severity does not change the messages that are forwarded to syslog.
FACILITY
Specifies what type of application is logging the message. The default is Internal (aka Syslog). This is used to categorize the messages when they are received by the Syslog server.
Click on Test Connection to test the IP/DOMAIN, PORT, AND PROTOCOL settings. If you entered valid values, after a couple of moments, you should see a success confirmation popup:
Field Reference
Rules
Rule | Definition |
|---|---|
ScriptControl Alert | Detects Script Control alerts from Cylance endpoints |
Threat Quarantined | Alerts if a threat is quarantined by Cylance |
Threat Found | Alerts if Cylance detects a threat |
ScriptControl Blocked | Detects if Script Control blocks an action |
Threat Cleared | Alerts if Cylance clears a threat |
Threat Changed | Alerts if Cylance detects that a threat has changed |
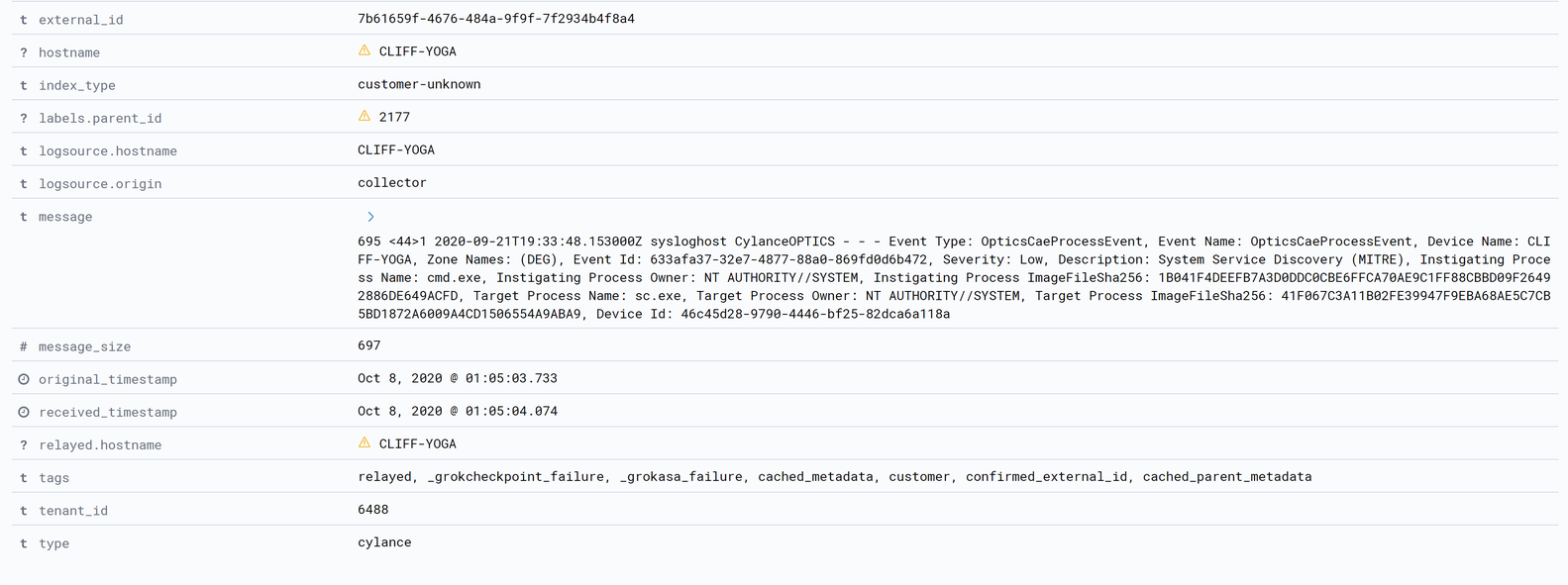
Optics Process Event | Alerts if Cylance optics detects a process event |
Optics File Event | Alerts if Cylance optics detects a file event |
Optics Registry Event | Alerts if Cylance optics detects a registry event |
