AWS GuardDuty
Amazon GuardDuty is a threat detection service that continuously monitors for malicious activity and unauthorized behavior to protect your AWS accounts, workloads, and data stored in Amazon S3. With the cloud, the collection and aggregation of account and network activities is simplified, but it can be time consuming for security teams to continuously analyze event log data for potential threats. With GuardDuty, you now have an intelligent and cost-effective option for continuous threat detection in AWS. The service uses machine learning, anomaly detection, and integrated threat intelligence to identify and prioritize potential threats. GuardDuty analyzes tens of billions of events across multiple AWS data sources, such as AWS CloudTrail event logs, Amazon VPC Flow Logs, and DNS logs. With a few clicks in the AWS Management Console, GuardDuty can be enabled with no software or hardware to deploy or maintain. By integrating with Amazon CloudWatch Events, GuardDuty alerts are actionable, easy to aggregate across multiple accounts, and straightforward to push into existing event management and workflow systems
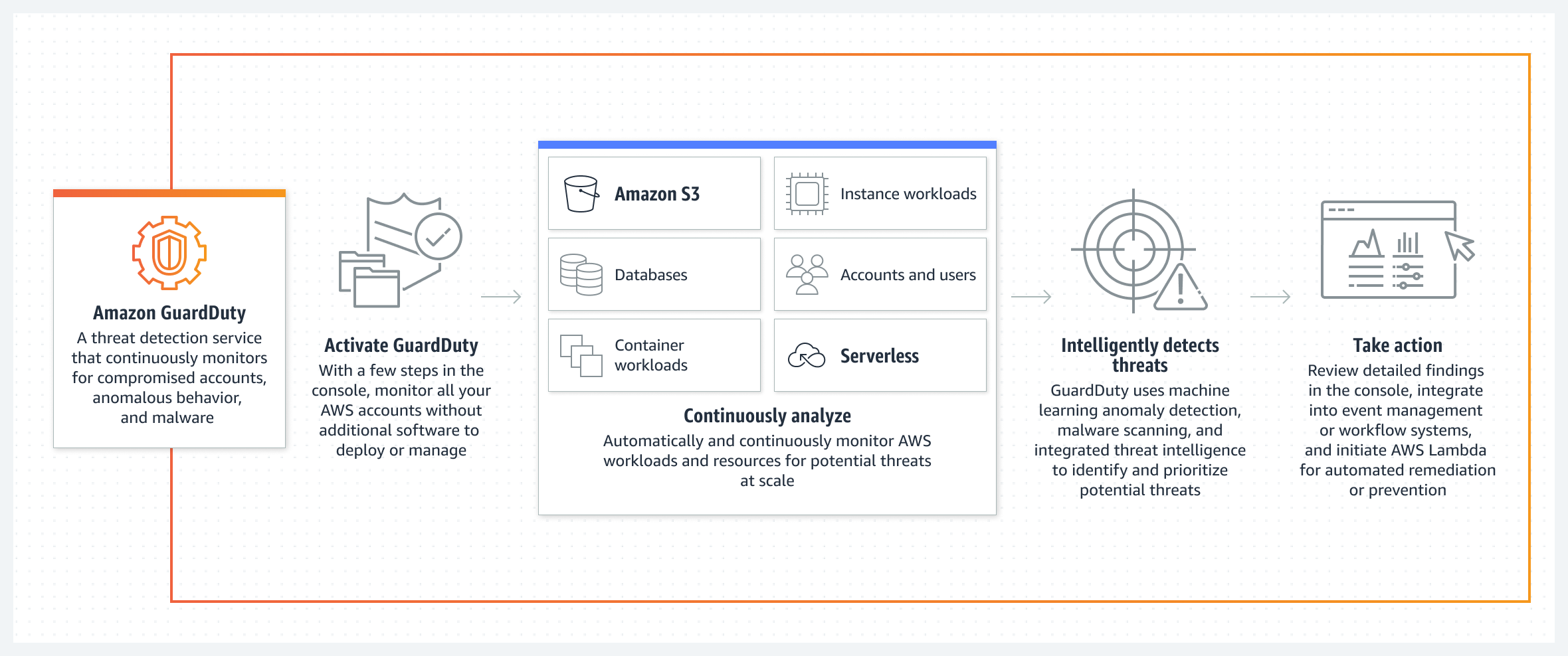
How It Works
Topics Discussed
Benefits
Comprehensive threat identification
Amazon GuardDuty identifies threats by continuously monitoring the network activity, data access patterns, and account behavior within the AWS environment. GuardDuty comes integrated with up-to-date threat intelligence feeds from AWS, CrowdStrike, and Proofpoint. Threat intelligence coupled with machine learning and behavior models help you detect activity such as crypto-currency mining, credential compromise behavior, unauthorized and unusual data access, communication with known command-and-control servers, or API calls from known malicious IPs.
Strengthens security through automation
In addition to detecting threats, Amazon GuardDuty also makes it easy to automate how you respond to threats, reducing your remediation and recovery time. GuardDuty can perform automated remediation actions by leveraging Amazon CloudWatch events and AWS Lambda. GuardDuty security findings are informative and actionable for security operations. The findings include the affected resource's details and attacker information, such as IP address and geo-location.
Enterprise scale and central management
Amazon GuardDuty provides multi-account support using AWS Organizations, so you can enable GuardDuty across all of your existing and new accounts. Your security team can aggregate your organization's findings across accounts into a single GuardDuty administrator account for easier management. The aggregated findings are also available through CloudWatch Events, making it easy to integrate with an existing enterprise event management system.
You can use this document to collect and send AWS GuardDuty logs to Armor's Security Information & Event Management (SIEM).
Pre-Deployment Considerations
Before you begin, review the following requirements:
AWS Account Information
AWS Account Number
AWS Access Key
AWS Secret Key
This action will be described in a later step.
AWS Account Permissions (Policies)
AWS GuardDuty
AWS Lambda
AWS CloudWatch
AWS CloudFormation
Permissions
Write Virtual Machine
Delete Log Management
Read Log Endpoints
Read Log Relays
Write Log Relays
Delete Log Relays
To learn more about permissions, see Roles and Permissions.
Supported AWS GuardDuty Regions
Armor's SIEM supports the following AWS GuardDuty regions:
Armor does not provide support for using AWS CloudFormation to set up AWS GuardDuty resources in AWS GovCloud (US).
Log Relay
To learn how to add Log Relay to your account, see Obtain Log Relay for Remote Log Collection.
Update Your AWS Permissions
Based on the status of your AWS service account (existing or non-existing), review the appropriate option.
According to AWS, "An IAM user is a resource in IAM that has associated credentials and permissions. An IAM user can represent a person or an application that uses its credentials to make AWS requests. This is typically referred to as a service account."
Option 1: For existing AWS service accounts
AWS GuardDuty
AWS Lambda
AWS CloudWatch
AWS CloudFormation
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"logs:Describe*",
"logs:Get*",
"logs:List*",
"logs:StartQuery",
"logs:StopQuery",
"logs:TestMetricFilter",
"logs:FilterLogEvents"
],
"Resource": [
"arn:aws:logs:*:*:log-group:Armor_GuardDuty_Log_Group",
"arn:aws:logs:*:*:log-group:Armor_GuardDuty_Log_Group:*",
"arn:aws:logs:*:*:log-group:Armor_GuardDuty_Log_Group:*:*"
],
"Effect": "Allow"
}
]
}
Option 2: For non-existing AWS service accounts
AWS is in the process of updating the screens in their AWS console. As a result, there are two versions of the AWS CloudFormation screen; however, this step is compatible with both views.
Click the following link to create a service account in AWS:
Click Next.
Click Next.
Click Next.
At the bottom of the screen, mark the box to accept the terms, and then click Create stack or Create.
The service account will take a few minutes to create; you may need to refresh the screen to see account updates.
Note the name of the newly created service account.
Retrieve Your AWS Credentials
AWS account number / account ID
AWS Access Key
AWS Secret Key
In a later step, you will add this information to your account.
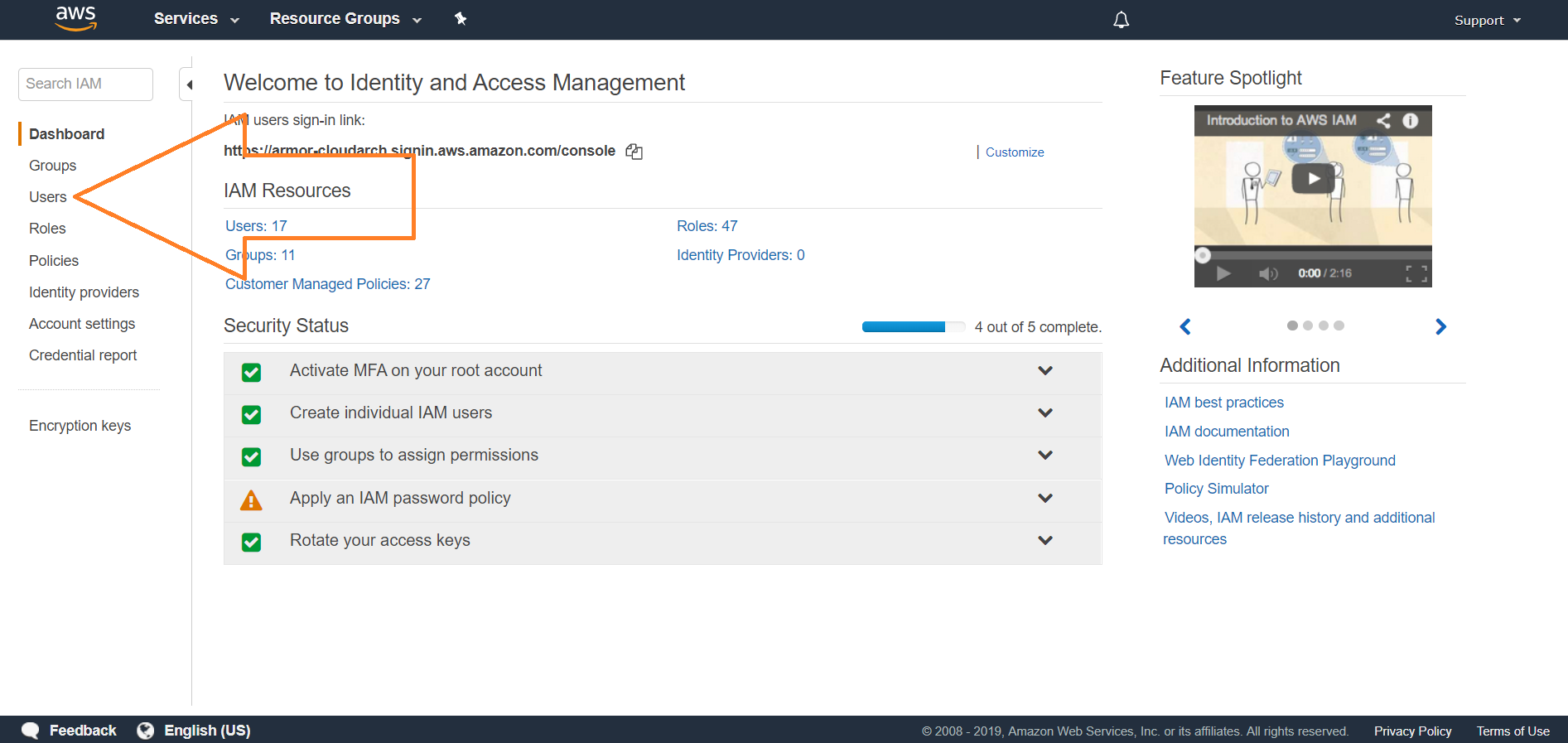
In your AWS console, access the IAM section.
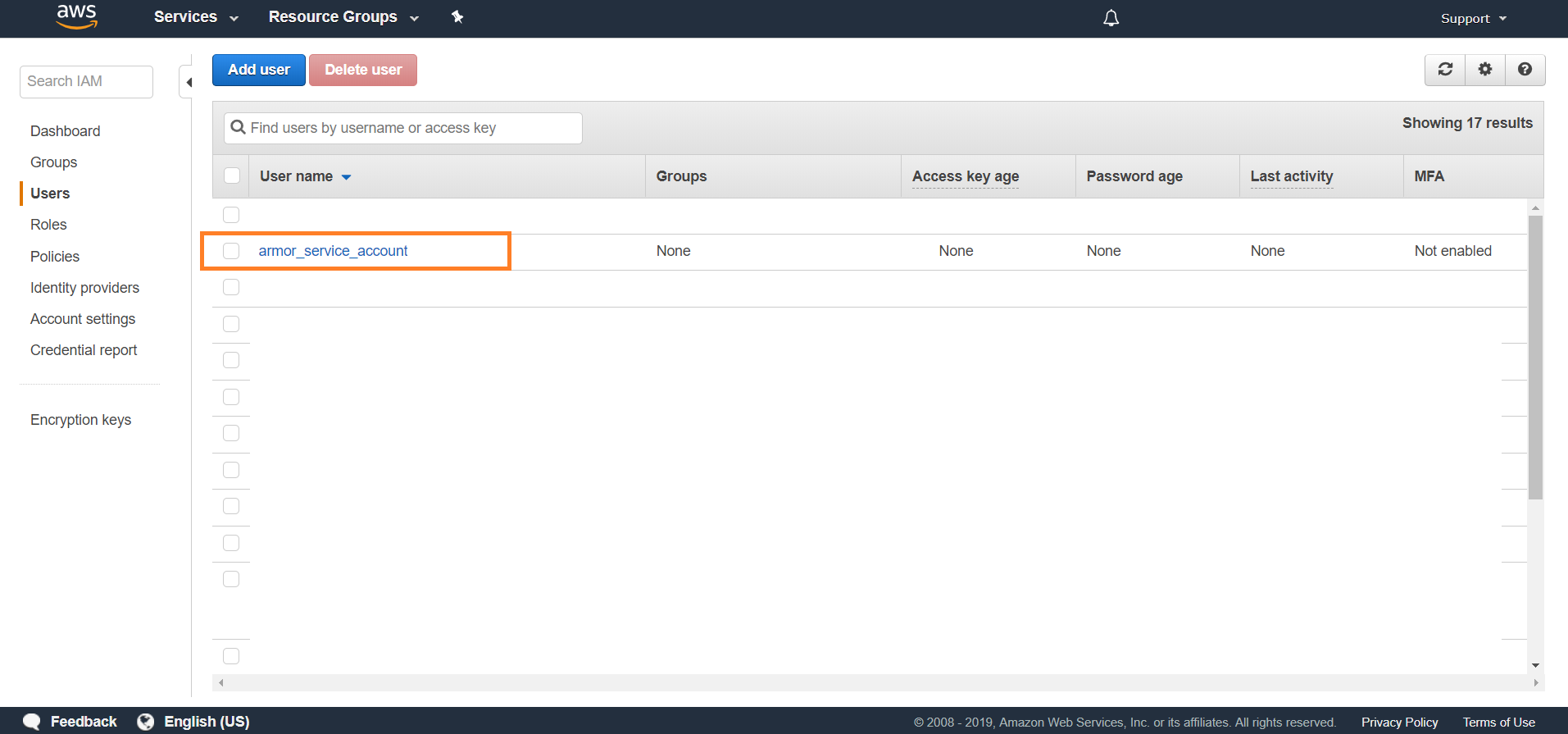
Locate and select the service account.
Click Security credentials.
Click Create access key.
In the window that appears, copy your Access key ID and Secret access key. You will enter these keys in Nexus in a later step.
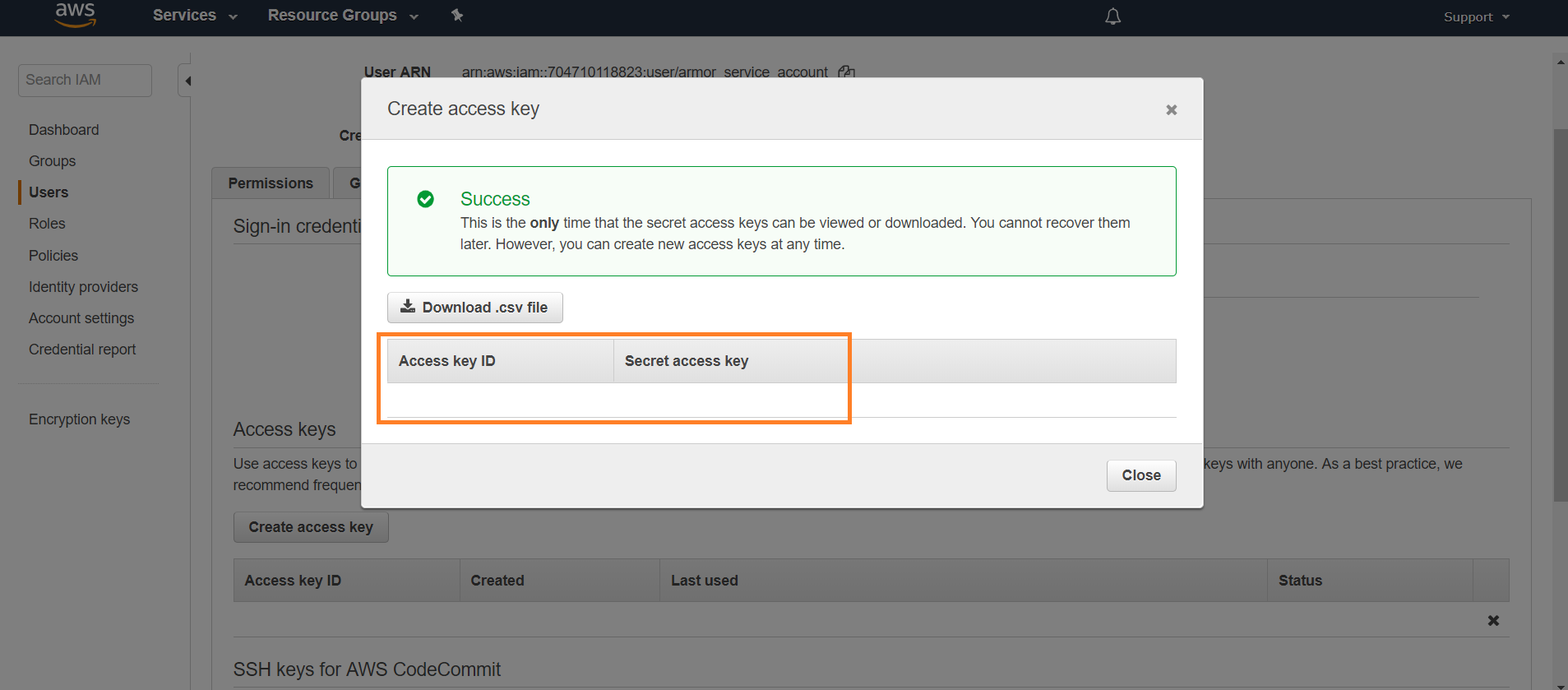
To learn more about your keys, especially how to create a key, please visit AWS's documentation site.
Create A Remote Log Source Type
In Nexus, hover over Threat Management
 on the left-side nav.
on the left-side nav. Click Log Search.
Click External Sources.
Click the plus sign
 .
. If you do not have any log sources already created, then click Add a New Log Source.
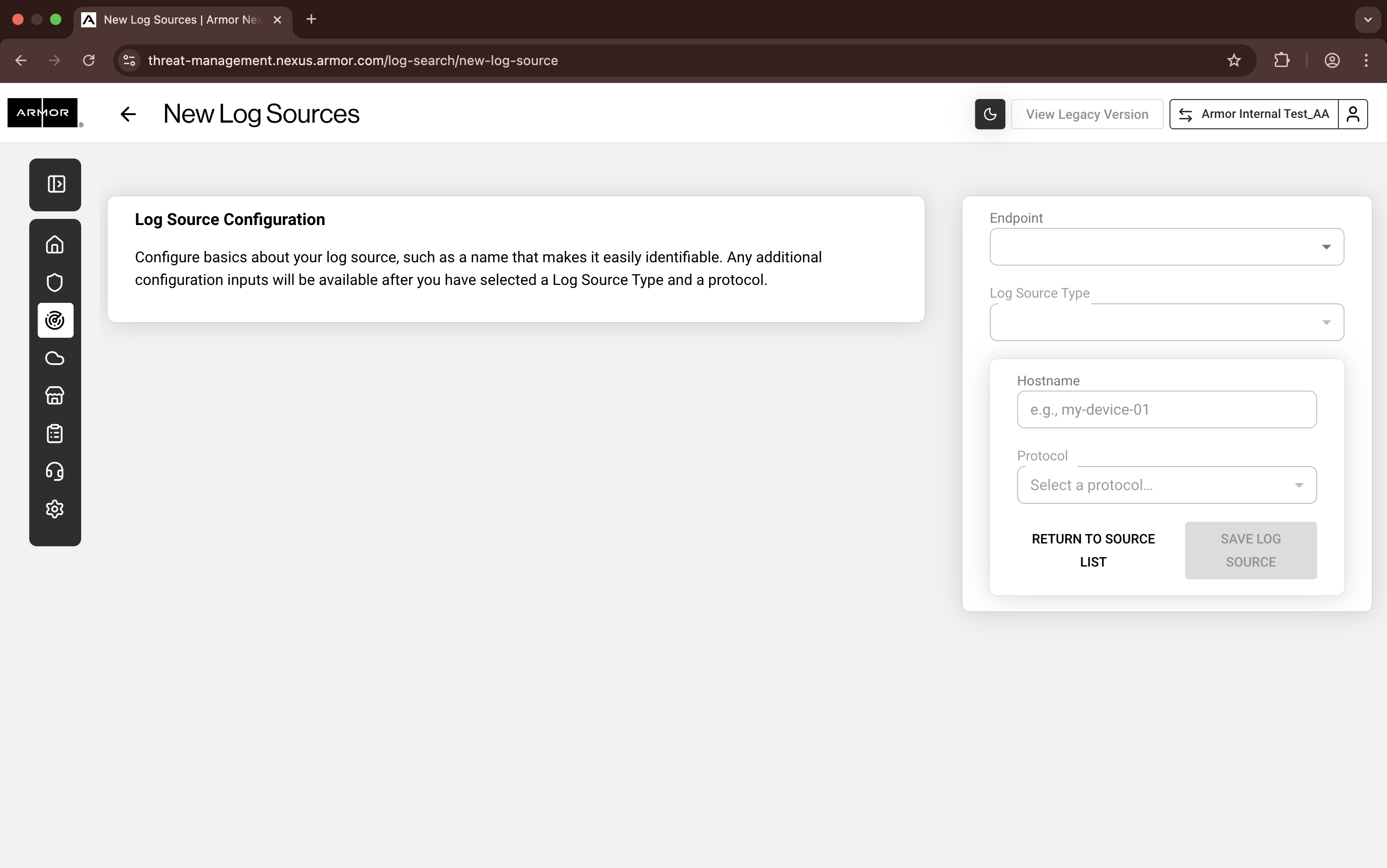
Nexus - Add New Log Sources
Complete the missing fields:
In Endpoint, use the drop-down menu to select an already-configured endpoint.
In Log Source Type, click Amazon GuardDuty.
By default, Hostname will be populated; however, the Hostname will change after you enter your AWS credentials.
By default, Protocol will be populated.
Enter your AWS information.
In AWS Account Number, paste the AWS account number for your service account. You must remove any dashes or hyphens ( - ).
In AWS Access Key and AWS Secret Key, enter the key information for your service account.
Under AWS Regions, click Select All Regions.
For best practices, Armor and AWS recommend that you select every region.
Click Save Log Source.
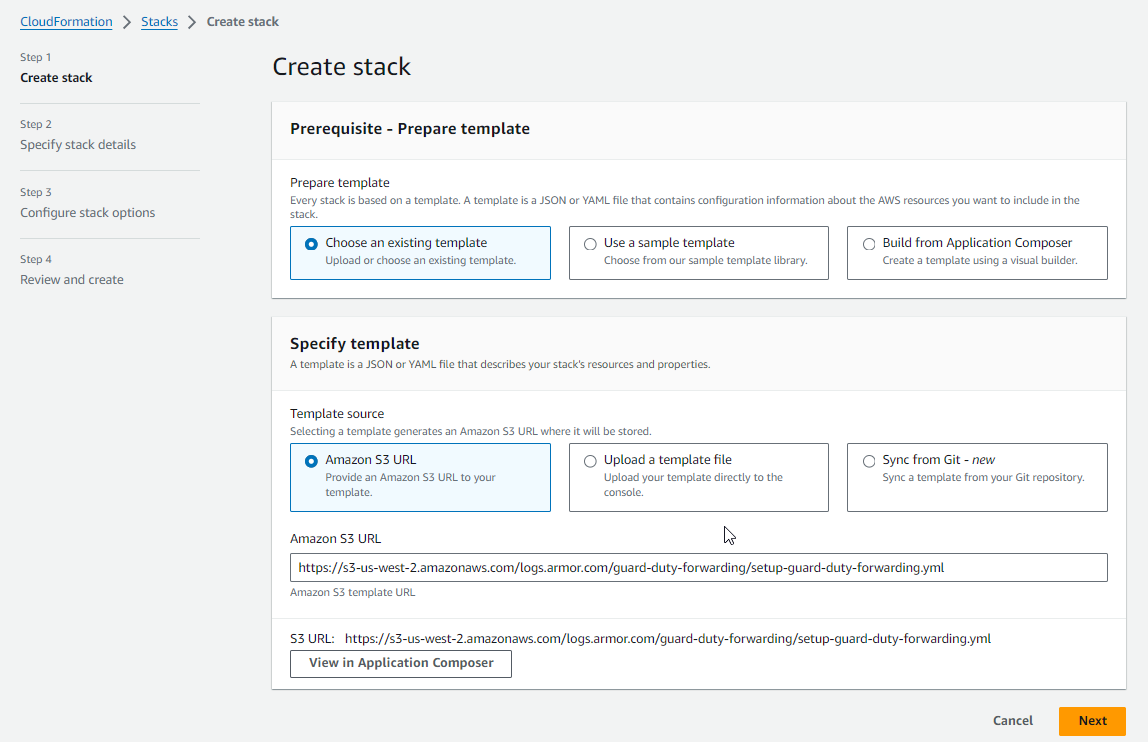
In the window that appears, click the link to directly access your AWS account with Armor's CloudFormation StackSet or Stack template already imported.
MULTIPLE REGIONS | TO COLLECT AND SEND LOGS FROM MULTIPLE REGIONS, CLICK THIS LINK. AFTERWARDS, SEE STEP 4. ARMOR AND AWS RECOMMEND THAT YOU CONFIGURE YOUR ACCOUNT TO SEND LOGS FROM ALL REGIONS. use the following Amazon S3 URL if not auto populated: https://s3-us-west-2.amazonaws.com/logs.armor.com/guard-duty-forwarding/setup-guard-duty-forwarding.yml | |
|---|---|---|
SINGLE REGION | TO COLLECT AND SEND LOGS FROM A SINGLE REGION, CLICK THIS LINK. AFTERWARDS, SEE STEP 5. |
Configure the AWS GuardDuty CloudFormation StackSet Template for Multiple Regions
If you only want to send logs from one region, then see Configure the AWS GuardDuty CloudFormation Stack Template.
Click on the link below to create a CloudFormation StackSet:
https://console.aws.amazon.com/cloudformation/home#/stacksets/new?stackSetName=guard-duty-forwarding&templateURL=https:%2F%2Fs3-us-west-2.amazonaws.com%2Flogs.armor.com%2Fguard-duty-forwarding%2Fsetup-guard-duty-forwarding.ymlFor multiregional , under Permissions, in the drop-down menu, select AWSCloudFormationStackSetExecutionRole, if it’s not done already, please Grant self-managed permissions
In Specify template/Amazon S3 URL, verify that the displayed link is: https://s3-us-west-2.amazonaws.com/logs.armor.com/guard-duty-forwarding/setup-guard-duty-forwarding.yml
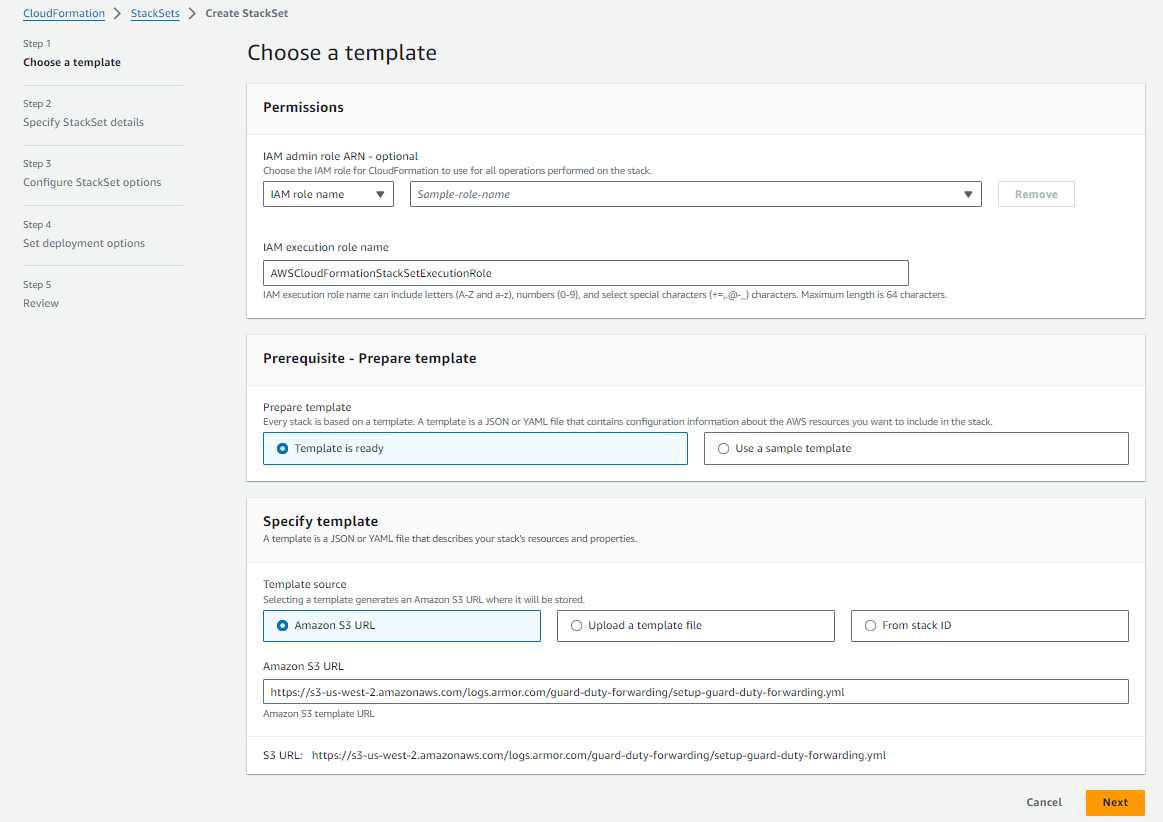
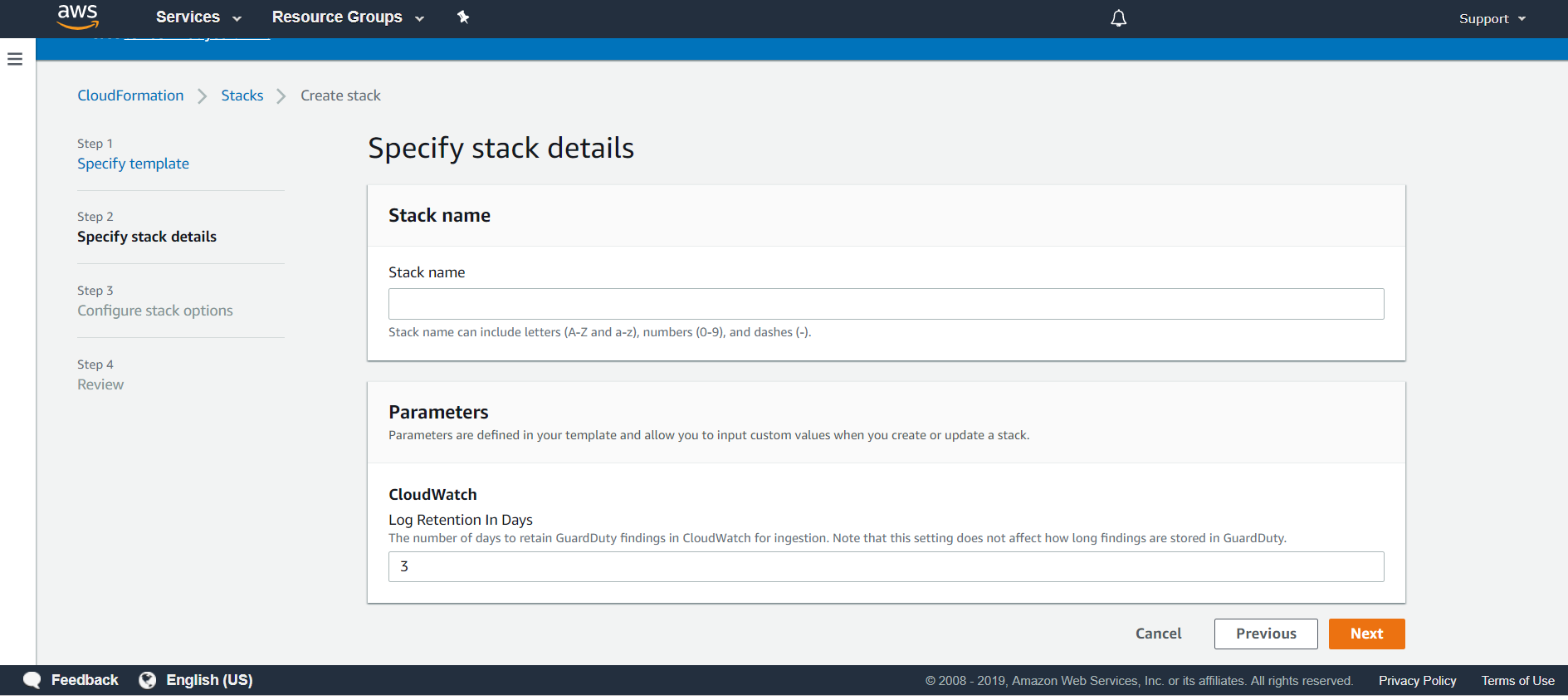
(Required) In StackSet name, enter a descriptive name for the stack set.
This name must begin with a letter, and can only contain letters, numbers, and hyphens.
In Log Retention In Days, specify the number of days to maintain logs.
By default, Armor has configured 3 days.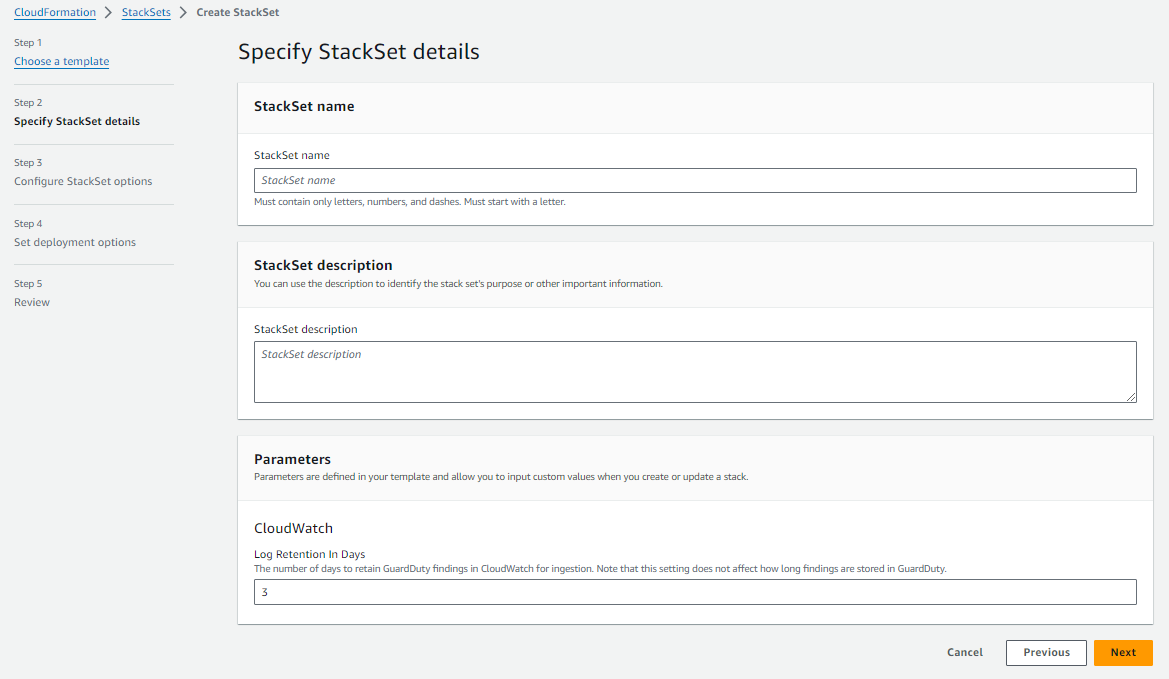
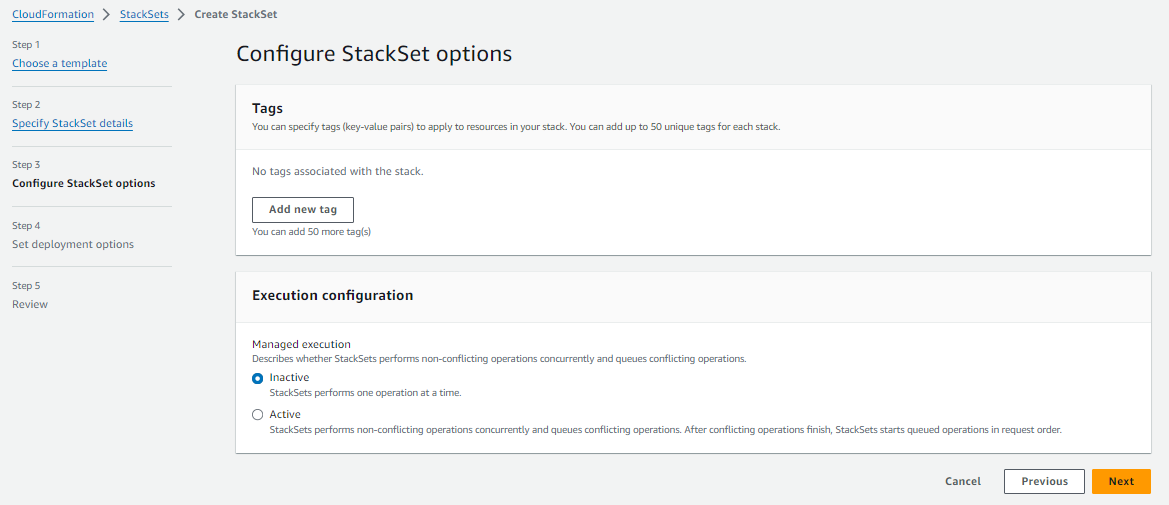
(Optional) If required by your organization, under Tags, add your organization's tags to the CloudFormation deployment.
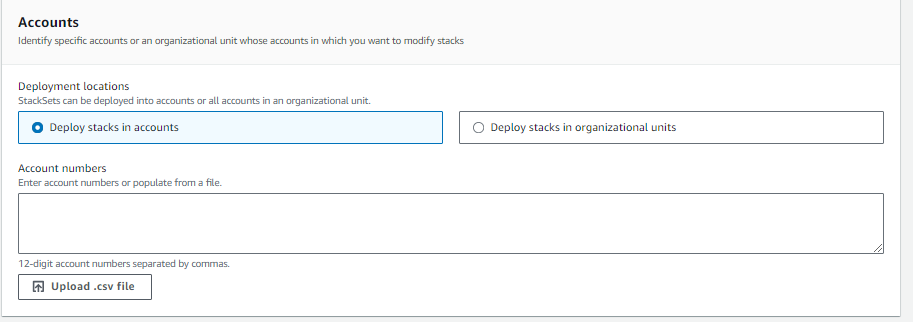
In the Set deployment options/Accounts, enter the AWS account number for the AWS service account.
This is the same AWS service account number that you previously entered in Nexus.
You must remove any dashes or hyphens ( - ).
In the Set deployment options/Specify regions, add the desired region(s) for log collection.
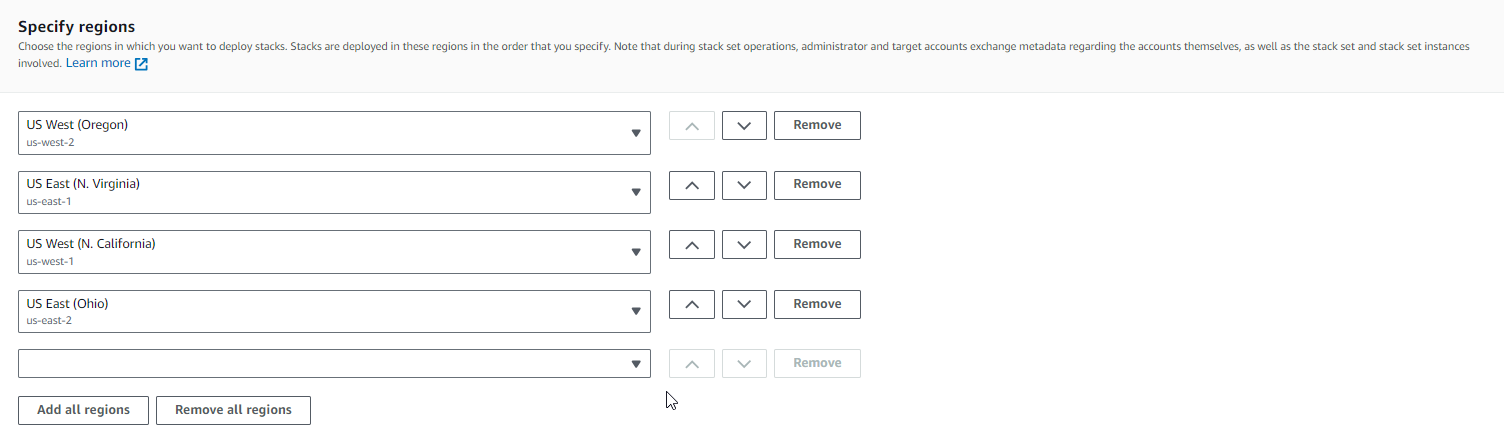
Click Next.
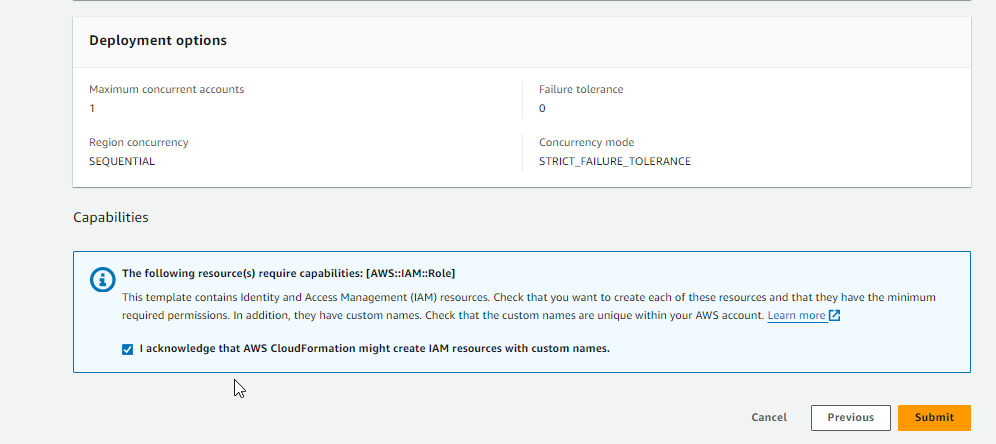
At the bottom of the screen, mark the box to accept the terms, and then click Submit.
(Optional) Configure the AWS GuardDuty CloudFormation Stack Template for a Single Region
Verify Connection
In Nexus, hover over Threat Management
 on the left-side nav.
on the left-side nav. Click Log Search.
Click External Sources.
Locate the newly created remote log source.
Under Last Event, verify that a recent activity took place.
This status will indicate that the configurations were successful.
After you update your AWS account, it may take 30 minutes to display the updates.
Then click Log Search.
In the search field, enter your AWS account number surrounded by asterisks wildcards.
For example, you can enter *123456789123*
This action will display collected AWS CloudTrail logs.
Troubleshooting
If you are having issues adding a remote collector to an AWS GuardDuty remote device, consider that:
You do not have proper permissions in AWS.
You entered the AWS account information for an incorrect AWS service account.
If you have multiple AWS accounts, especially child or organization accounts, you must verify that you added the service account information for the correct service account
Edit A Stack
This section only applies to single stacks, not stack sets.
Currently, you cannot edit an existing stack in Nexus. If you want to update your stack, then you must delete the remote log source, and then create a new one with your desired updates.