Create a Remote Log Source - Palo Alto Firewall
Topics Discussed
You can use this document to add a remote log collector to a Palo Alto Firewall remote device (log source).
Pre-deployment considerations
Before you begin, review the following requirements:
Log Relay
For remote log collection, you must have a Log Relay server on your account.
To learn how to add Log Relay to your account, see Obtain Log Relay for Remote Log Collection.
Assumptions
The firewall is running PAN-OS version 8.1.x
The device is already set up and configured with the security policies that are needed
You are allowing traffic through TCP port 10206
Forwarding traffic logs from a Palo Alto Networks firewall to a syslog server has four main steps:
Create a syslog server profile
Create a log forwarding profile
Use the log forwarding profile in your security policy
Commit the changes
The documentation below outlines steps 1-3.
Create a Syslog Server Profile
Log into the Palo Alto console.
Select Device, then select Server Profiles, followed by Syslog.
In the bottom left-side of the screen, click Add to create a new server profile.
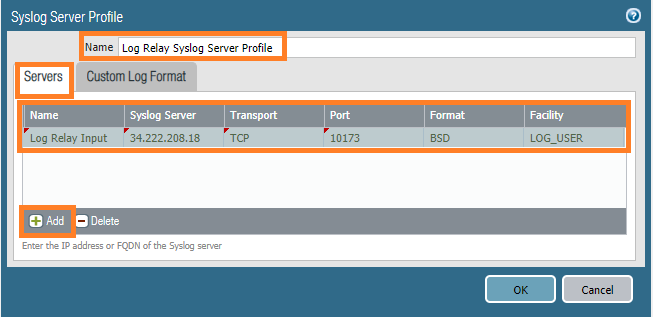
In the Syslog Server Profile window, in the Name field, enter Log Relay Syslog Server Profile.
Click Servers, then click Add to create a new server.
Name the server Log Relay Input.
In Syslog Server, input the IP address of the log relay.
Set the Transport to TCP.
Set the Port to 10206.
Set the Format to BSD.
Set the Facility to LOG_USER.
On the Custom Log Format tab, change the Custom Format of each log type to the text provided in the table below.
Be sure to remove any newlines from the formatting before entering the text into the configuration files.
Log Type Custom Format Wildfire LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$threatid|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|Miscellaneous=$misc|ThreatID=$threatid|URLCategory=$category|sev=$number-of-severity|Severity=$severity|Direction=$direction|sequence=$seqno|ActionFlags=$actionflags|SourceLocation=$srcloc|DestinationLocation=$dstloc|ContentType=$contenttype|PCAP_ID=$pcap_id|FileDigest=$filedigest|Cloud=$cloud|URLIndex=$url_idx|RequestMethod=$http_method|FileType=$filetype|Sender=$sender|Subject=$subject|Recipient=$recipient|ReportID=$reportid|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|SrcUUID=$src_uuid|DstUUID=$dst_uuid|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel|ThreatCategory=$thr_category|ContentVer=$contentver User-ID LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$subtype|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|FactorType=$factortype|VirtualSystem=$vsys|DataSourceName=$datasourcename|DataSource=$datasource|DataSourceType=$datasourcetype|FactorNumber=$factorno|VirtualSystemID=$vsys_id|TimeoutThreshold=$timeout|src=$ip|srcPort=$beginport|dstPort=$endport|RepeatCount=$repeatcnt|usrName=$user|sequence=$seqno|EventID=$eventid|FactorCompletionTime=$factorcompletiontime|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|ActionFlags=$actionflags URL Filtering LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$threatid|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|Miscellaneous=$misc|ThreatID=$threatid|URLCategory=$category|sev=$number-of-severity|Severity=$severity|Direction=$direction|sequence=$seqno|ActionFlags=$actionflags|SourceLocation=$srcloc|DestinationLocation=$dstloc|ContentType=$contenttype|PCAP_ID=$pcap_id|FileDigest=$filedigest|Cloud=$cloud|URLIndex=$url_idx|RequestMethod=$http_method|UserAgent=$user_agent|identSrc=$xff|Referer=$referer|Subject=$subject|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|SrcUUID=$src_uuid|DstUUID=$dst_uuid|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel|ThreatCategory=$thr_category|ContentVer=$contentver Tunnel Inspection LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$action|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|sequence=$seqno|ActionFlags=$actionflags|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel|totalBytes=$bytes|dstBytes=$bytes_received|srcBytes=$bytes_sent|totalPackets=$packets|dstPackets=$pkts_received|srcPackets=$pkts_sent|MaximumEncapsulation=$max_encap|UnknownProtocol=$unknown_proto|StrictChecking=$strict_check|TunnelFragment=$tunnel_fragment|SessionsCreated=$sessions_created|SessionsClosed=$sessions_closed|SessionEndReason=$session_end_reason|ActionSource=$action_source|startTime=$start|ElapsedTime=$elapsed Traffic LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$action|cat=$type|ReceiveTime=$receive_time|SerialNumber=$serial|Type=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|totalBytes=$bytes|dstBytes=$bytes_received|srcBytes=$bytes_sent|totalPackets=$packets|StartTime=$start|ElapsedTime=$elapsed|URLCategory=$category|sequence=$seqno|ActionFlags=$actionflags|SourceLocation=$srcloc|DestinationLocation=$dstloc|dstPackets=$pkts_received|srcPackets=$pkts_sent|SessionEndReason=$session_end_reason|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|ActionSource=$action_source|SrcUUID=$src_uuid|DstUUID=$dst_uuid|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel Threat LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$threatid|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|Miscellaneous=$misc|ThreatID=$threatid|URLCategory=$category|sev=$number-of-severity|Severity=$severity|Direction=$direction|sequence=$seqno|ActionFlags=$actionflags|SourceLocation=$srcloc|DestinationLocation=$dstloc|ContentType=$contenttype|PCAP_ID=$pcap_id|FileDigest=$filedigest|Cloud=$cloud|URLIndex=$url_idx|RequestMethod=$http_method|Subject=$subject|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|SrcUUID=$src_uuid|DstUUID=$dst_uuid|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel|ThreatCategory=$thr_category|ContentVer=$contentver System LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$eventid|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|VirtualSystem=$vsys|Filename=$object|Module=$module|sev=$number-of-severity|Severity=$severity|msg=$opaque|sequence=$seqno|ActionFlags=$actionflags|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name SCTP LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$action|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|genTime=$time_generated|src=$src|dst=$dst|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|proto=$proto|action=$action|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vsysName=$vsys_name|DeviceName=$device_name|sequence=$seqno|AssocID=$assoc_id|PayloadProtoID=$ppid|sev=$num_of_severity|SCTPChunkType=$sctp_chunk_type|SCTPVerTag1=$verif_tag_1|SCTPVerTag2=$verif_tag_2|SCTPCauseCode=$sctp_cause_code|DiamAppID=$diam_app_id|DiamCmdCode=$diam_cmd_code|DiamAVPCode=$diam_avp_code|SCTPStreamID=$stream_id|SCTPAssEndReason=$assoc_end_reason|OpCode=$op_code|CPSSN=$sccp_calling_ssn|CPGlobalTitle=$sccp_calling_gt|SCTPFilter=$sctp_filter|SCTPChunks=$chunks|SrcSCTPChunks=$chunks_sent|DstSCTPChunks=$chunks_received|Packets=$packets|srcPackets=$pkts_sent|dstPackets=$pkts_received HIP Match LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$matchname|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|usrName=$srcuser|VirtualSystem=$vsys|identHostName=$machinename|OS=$os|identsrc=$src|HIP=$matchname|RepeatCount=$repeatcnt|HIPType=$matchtype|sequence=$seqno|ActionFlags=$actionflags|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|VirtualSystemID=$vsys_id|srcipv6=$srcipv6|startTime=$cef-formatted-time_generated Data LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$threatid|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|src=$src|dst=$dst|srcPostNAT=$natsrc|dstPostNAT=$natdst|RuleName=$rule|usrName=$srcuser|SourceUser=$srcuser|DestinationUser=$dstuser|Application=$app|VirtualSystem=$vsys|SourceZone=$from|DestinationZone=$to|IngressInterface=$inbound_if|EgressInterface=$outbound_if|LogForwardingProfile=$logset|SessionID=$sessionid|RepeatCount=$repeatcnt|srcPort=$sport|dstPort=$dport|srcPostNATPort=$natsport|dstPostNATPort=$natdport|Flags=$flags|proto=$proto|action=$action|Miscellaneous=$misc|ThreatID=$threatid|URLCategory=$category|sev=$number-of-severity|Severity=$severity|Direction=$direction|sequence=$seqno|ActionFlags=$actionflags|SourceLocation=$srcloc|DestinationLocation=$dstloc|ContentType=$contenttype|PCAP_ID=$pcap_id|FileDigest=$filedigest|Cloud=$cloud|URLIndex=$url_idx|RequestMethod=$http_method|Subject=$subject|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|SrcUUID=$src_uuid|DstUUID=$dst_uuid|TunnelID=$tunnelid|MonitorTag=$monitortag|ParentSessionID=$parent_session_id|ParentStartTime=$parent_start_time|TunnelType=$tunnel|ThreatCategory=$thr_category|ContentVer=$contentver Correlation LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|8.0|$category|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|devTime=$cef-formatted-receive_time|startTime=$cef-formatted-time_generated|Severity=$severity|VirtualSystem=$vsys|VirtualSystemID=$vsys_id|src=$src|SourceUser=$srcuser|msg=$evidence|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|ObjectName=$object_name|ObjectID=$object_id Config LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$result|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|devTime=$cef-formatted-receive_time|src=$host|VirtualSystem=$vsys|msg=$cmd|usrName=$admin|client=$client|Result=$result|ConfigurationPath=$path|sequence=$seqno|ActionFlags=$actionflags|BeforeChangeDetail=$before-change-detail|AfterChangeDetail=$after-change-detail|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name Authentication LEEF:1.0|Palo Alto Networks|PAN-OS Syslog Integration|$sender_sw_version|$event|ReceiveTime=$receive_time|SerialNumber=$serial|cat=$type|Subtype=$subtype|devTime=$cef-formatted-receive_time|ServerProfile=$serverprofile|LogForwardingProfile=$logset|VirtualSystem=$vsys|AuthPolicy=$authpolicy|ClientType=$clienttype|NormalizeUser=$normalize_user|ObjectName=$object|FactorNumber=$factorno|AuthenticationID=$authid|src=$ip|RepeatCount=$repeatcnt|usrName=$user|Vendor=$vendor|msg=$event|sequence=$seqno|DeviceGroupHierarchyL1=$dg_hier_level_1|DeviceGroupHierarchyL2=$dg_hier_level_2|DeviceGroupHierarchyL3=$dg_hier_level_3|DeviceGroupHierarchyL4=$dg_hier_level_4|vSrcName=$vsys_name|DeviceName=$device_name|AdditionalAuthInfo=$desc|ActionFlags=$actionflags 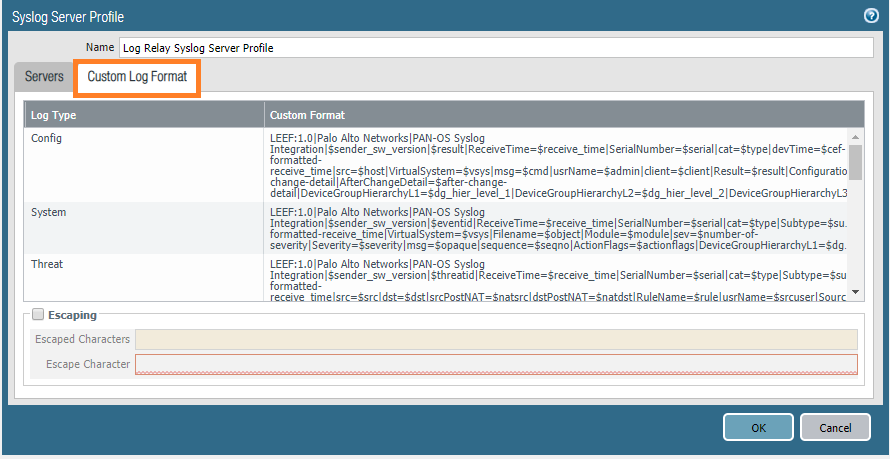
Click OK.
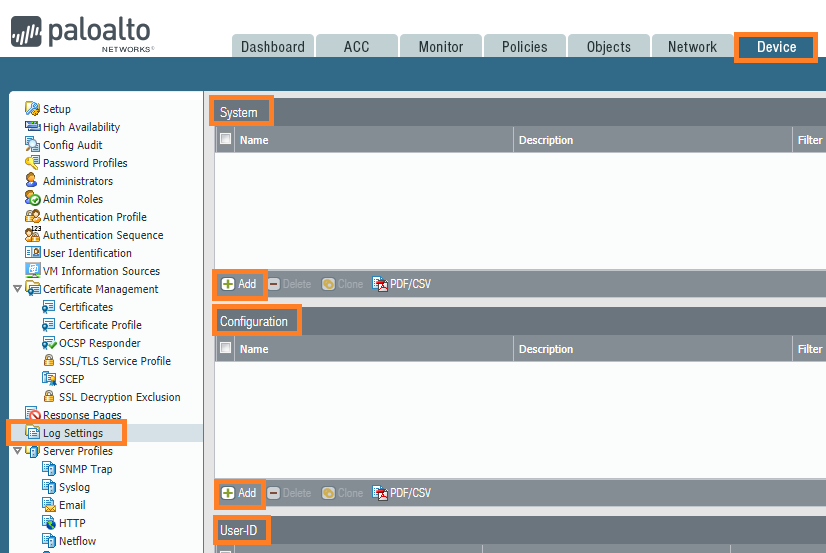
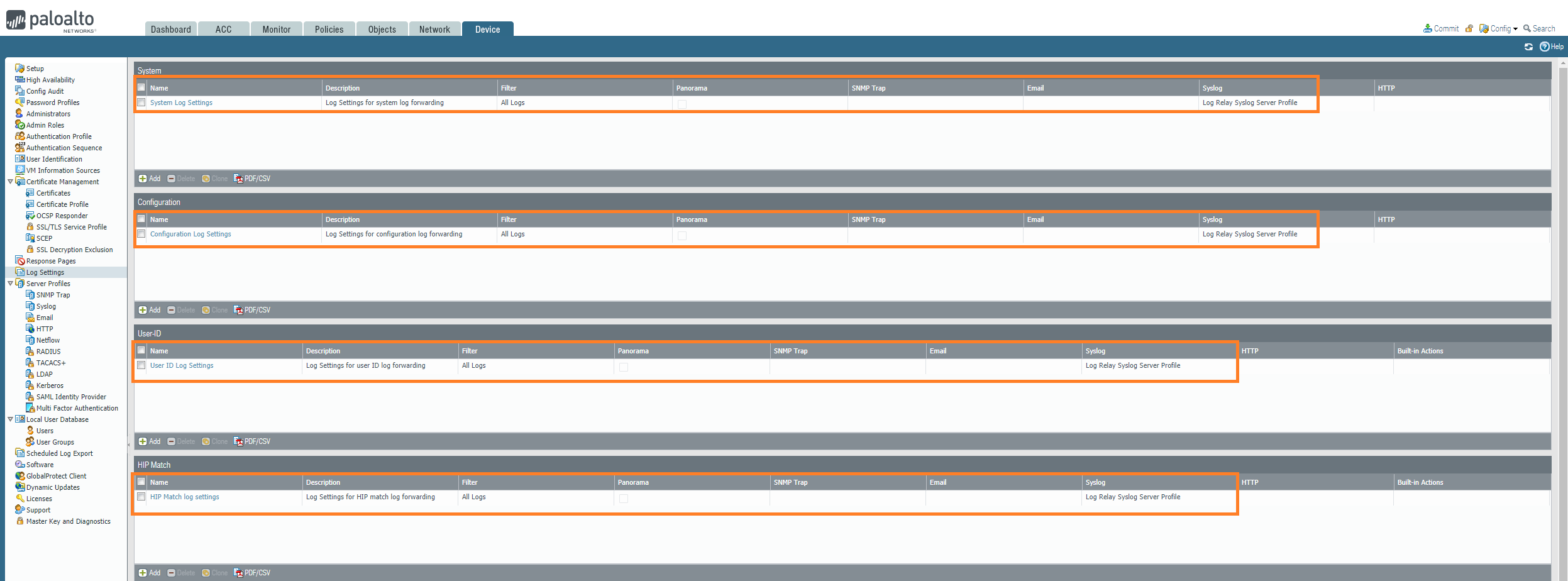
Select Device, then select Log Settings.
For each of the log types displayed (System, Configuration, User-ID, and HIP Match), click Add to add a new field to the table.
In Name, input a name that corresponds to the log type.
Set the Filter to All Logs.
In the Syslog window, click Add, then select the Log Relay Syslog Server Profile that you created in step 4.
Click OK.
Repeat steps 6-10 for each of the log types.
Create a Log Forwarding Profile
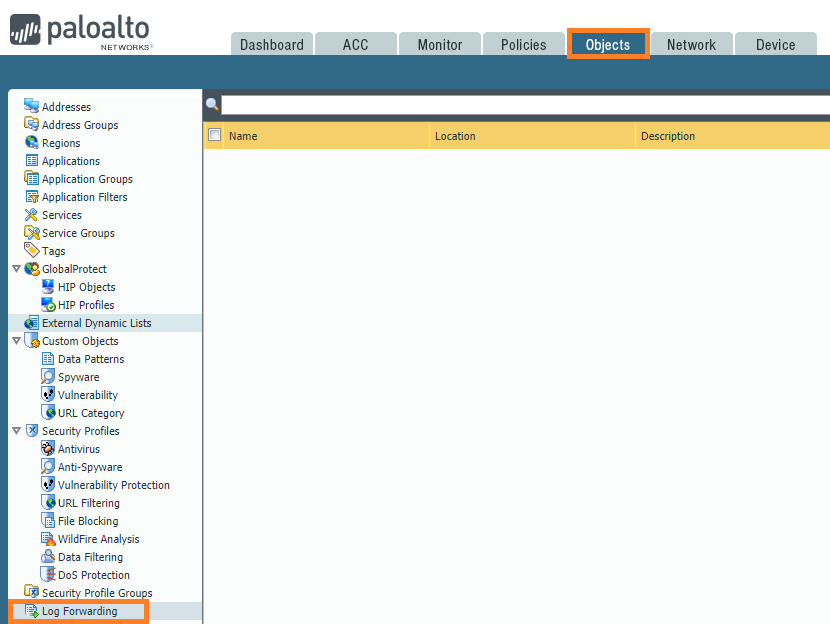
Select Objects, then select Log Forwarding.
In the bottom left-side of the screen, click Add to create a new Log Forwarding object.
In Name, enter Log Relay Forwarder.
Enter a description, indicating that this is the object that will be used to forward logs to the log relay.
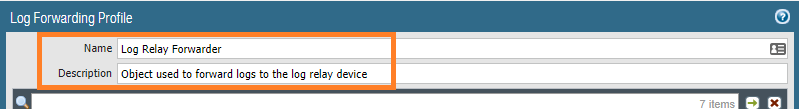
Click Add to add a new log relay policy.
In Name, enter Log Relay Auth.
Enter a description, indicating that this is the log forwarding match list that will be used for auth logs.
In Type, select auth.
Set the Filter to All Logs.
On the Syslog screen, click Add, then select the Log Relay Syslog Server Profile that you created in step 4.
Click OK.
Repeat steps 19-20 for each of the log types that are listed.
Change the titles and descriptions to match the corresponding log type.
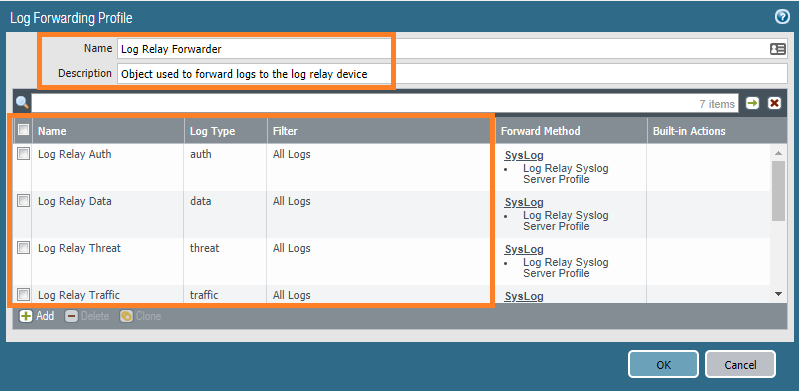
Select Network, then select Zones.
Modify each zone that is configured on the device:
In the Log Setting drop down menu, select Log Relay Forwarder.
Use the log forwarding profile in your security policy
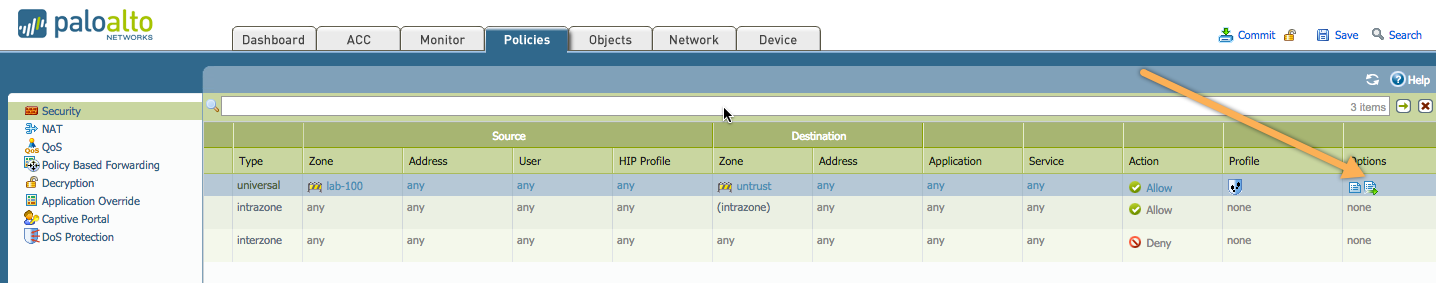
Go to Policies > Security
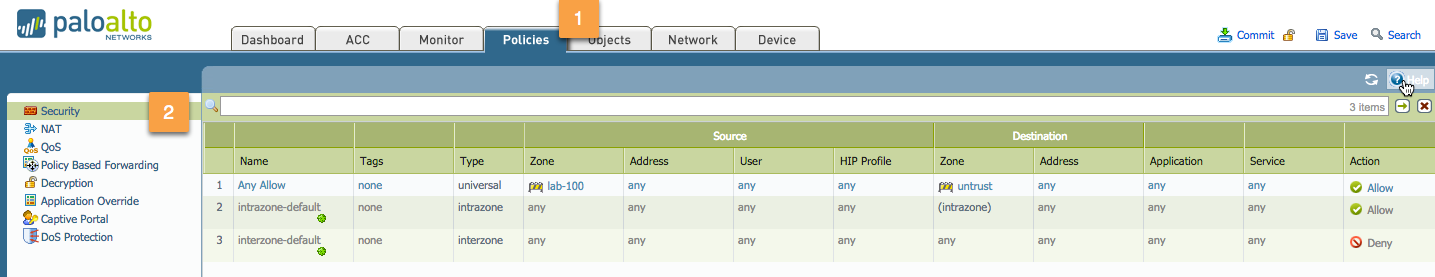
Select the rule for which the log forwarding needs to be applied (Any Allow) in the following example:
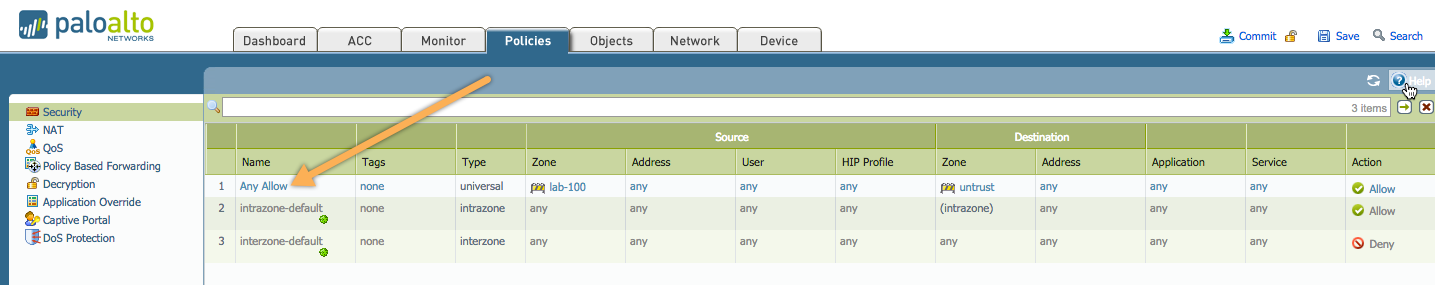
Next, go to the Actions tab, select Log Forwarding Profile from the dropdown, and click OK when you are happy with your configuration:
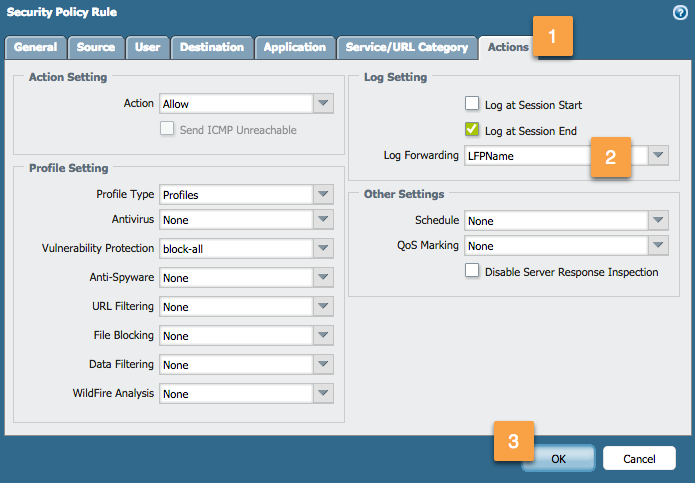
After clicking OK, you will notice the forwarding icon in the 'Options' column of your security rule: